利用iptables做nat传输数据卡死?
为了解决内外网访问问题,用一台ubuntu 14.04.1安装了
OpenVPN
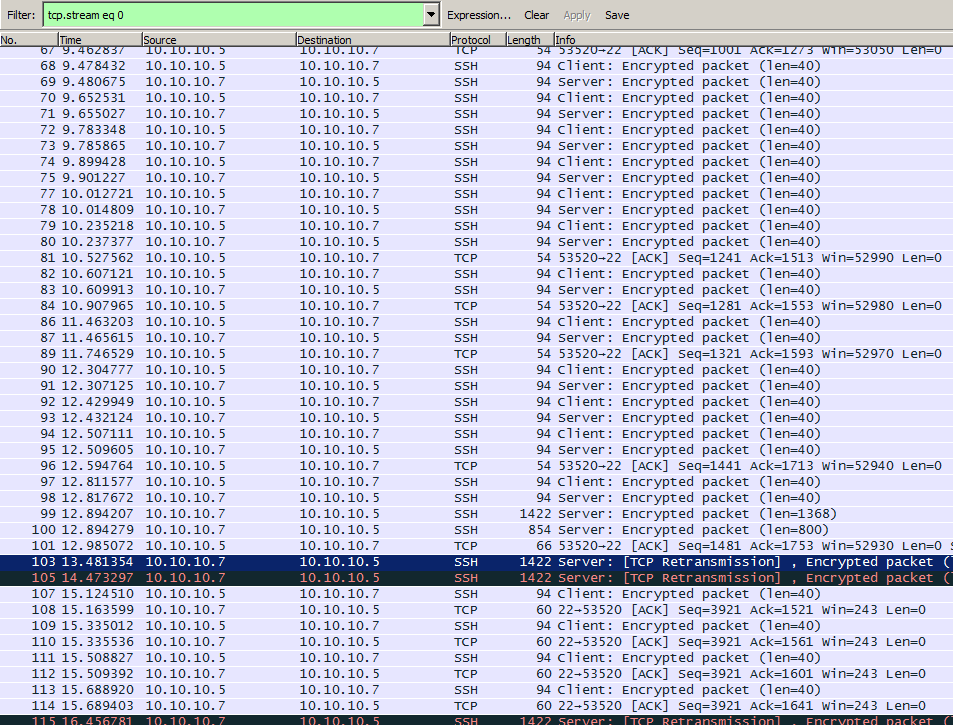
,并利用ubuntu自带的iptables做NAT。但是做完后发现,简单的远程访问没有问题,但是当数据返回稍微一大,如查看一个文件,或者传输一个文件时,访问终端就会吊死。但是利用iftop查看网络流量确是正常的。
网络结构如下:
shoper@~ % ifconfig 15-01-25 5:59 docker0 Link encap:Ethernet HWaddr 56:84:7a:fe:97:99 inet addr:172.17.42.1 Bcast:0.0.0.0 Mask:255.255.0.0 UP BROADCAST MULTICAST MTU:1500 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:0 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:0 (0.0 B) TX bytes:0 (0.0 B) eth0 Link encap:Ethernet HWaddr 00:50:56:b0:8a:0b inet addr:9.115.251.155 Bcast:9.115.251.255 Mask:255.255.255.0 inet6 addr: fe80::250:56ff:feb0:8a0b/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:11790 errors:0 dropped:0 overruns:0 frame:0 TX packets:1070 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:1010944 (1.0 MB) TX bytes:149870 (149.8 KB) eth1 Link encap:Ethernet HWaddr 00:50:56:b0:1c:a7 inet addr:10.10.10.5 Bcast:10.10.10.255 Mask:255.255.255.0 inet6 addr: fe80::250:56ff:feb0:1ca7/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:492 errors:0 dropped:0 overruns:0 frame:0 TX packets:104 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:60870 (60.8 KB) TX bytes:11280 (11.2 KB)
需求是从eth0访问的用户能够访问到eth1网络内的机器。
iptables的规则如下:
shoper@~ % cat /etc/iptables-rules 15-01-25 5:59 # Generated by iptables-save v1.4.21 on Tue Jan 6 06:00:25 2015 *nat :PREROUTING ACCEPT [1:78] :INPUT ACCEPT [1:78] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] :DOCKER - [0:0] -A PREROUTING -m addrtype --dst-type LOCAL -j DOCKER -A OUTPUT ! -d 127.0.0.0/8 -m addrtype --dst-type LOCAL -j DOCKER -A POSTROUTING -s 172.17.0.0/16 ! -o docker0 -j MASQUERADE -A POSTROUTING -o eth1 -j MASQUERADE COMMIT # Completed on Tue Jan 6 06:00:25 2015 # Generated by iptables-save v1.4.21 on Tue Jan 6 06:00:25 2015 *filter :INPUT ACCEPT [80:10140] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [69:6479] -A FORWARD -o docker0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A FORWARD -i docker0 ! -o docker0 -j ACCEPT -A FORWARD -i docker0 -o docker0 -j ACCEPT -A FORWARD -i eth1 -o eth0 -m state --state RELATED,ESTABLISHED -j ACCEPT # -A FORWARD -i eth1 -o eth0 -j ACCEPT -A FORWARD -i eth0 -o eth1 -j ACCEPT COMMIT # Completed on Tue Jan 6 06:00:25 2015
换了几台终端都是同样的问题。但是在这台ubuntu上向内网访问,或者是外网终端直接访问ubuntu却都没有问题,所以估计是iptables的问题。
不知sf上有人能帮到我么?